Getting started with Microsoft Azure Active Directory - B2C
Managing identity of an application is like an iceberg. On its face, it looks deceptively simple. Login, Logout... done. The complexity lies in aspects like scalability to millions of users, security, integration with social identity, password security, data breaches, and the list goes on...
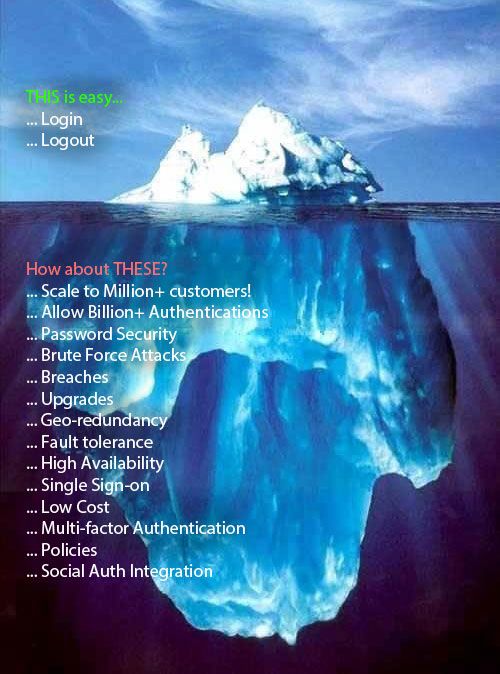
What if you could concentrate on the application logic instead of how the identity is to be managed and related complexities`?
Microsoft Azure Active Directory B2C (AD-B2C) does just that and a lot more.
By using Azure AD-B2C you can provide your customers:
- Easy sign ups.
- Self-service and password management.
- Single sign-on to all your apps.
- Social login using accounts, such as Facebook, Google+ or LinkedIn.
- OR, simply let them create a new username and password.
Steps to Create and use Azure B2C
Follow these steps to get started quickly.
- Create your B2C tenant
- Register your Application
- Create a Facebook Application
- Create a Google Application
- Test using your Signup Policy
- Click
All SettingsinAzure AD B2C Settings - Click on
Settings Blade>Sign-up policies - In Sign-up policies blade, click
Add - Provide a name and select all your Identity providers. Click
Create - Back in the
Sign-uppolicies select your policy. - Click
Run nowto test your integration.
The steps above shouldn't take you more than a couple of hours. (Actually, reading up might still take a little longer to improve your understanding, but setting it all up is fairly straight forward!). Just by doing as much, you now have got rid of all complexities mentioned in the image above. How cool is that?
Note
- Azure AD B2C is a pay-as-you-go Azure service.
- Apart from local accounts, the only supported providers at the moment are Facebook, Microsoft, Google, LinkedIn, and Amazon.
- You can use Azure AD Graph API to write your own migration tool that can help you migrate all your existing user names, passwords, and profiles to Azure AD B2C.
- Azure AD B2C doesn't work with SharePoint on-premises 2016 or Microsoft Dynamics, yet.
- Azure AD Connect is not designed to work with Azure AD B2C.
What next?
Stay tuned for upcoming articles. You may contact us for your software and consultancy requirements.